What will Web3 mean for cybersecurity?
What is Web3 and why is it happening?
At 33 years old, the internet has become both omnipresent in the lives of a vast number of people globally, and omniscient in the way it collects data on us, knows our preferences, our habits, our routines, location, personal information, and the things we like to watch and buy.
Meanwhile, the market monopolies of Web2 services and companies like Google (Alphabet), Facebook (Meta), Amazon, Apple and Microsoft have become omnipotent in that space. At the same time jurisdictional powers have been playing catch-up on the data protection implications of entities holding such vast amounts of privately stored, personal and payment information from a constantly growing global user base.
The Digital services Act was the EU’s response to exerting legislative powers over these companies, but there is a clear limit to the reach of the legislation outside of the EU’s influence, and while other regions have followed suit, the data collection and use or sale of data for targeted advertising has increased year after year. Nation states and jurisdictions have at times struggled to open dialogue and get messages across about internet safety and privacy concerns.
To give you a sense of the scale of Web2 companies According to The World Economic Forum, in 2019 43% of all internet traffic went through these services and within more specific categories, these monopolies can have an enormous share of the market such as Google having a whopping 87% of all internet search traffic.
If Web2 is served end delivered by large companies on private mega servers, proponents and early adopters say Web3 is the decentralised, democratised iteration of the web, with end-to-end encryption facilitated though blockchain technology between a vast network of connected users all providing the infrastructure and mechanism for the storage and transfer of data, assets, services, and applications.
Web3 is based on opensource software and trust in the end-to-end encryption of blockchain between all users of the network, decentralising data would have other impacts as well, for example when the servers of one of the market leaders goes down, millions, even billions of people can be affected. Likewise with data breaches from private servers via direct hack can affect enormous amounts of data and critical services in one go. The decentralised system is inherently a failsafe against that as if one ‘node’ or user goes offline there will be another to take its place immediately and so on.
When it was first mentioned in 2014 by one of the cryptocurrency Ethereum 2.0 creators, the idea was niche and underground, specific to cryptocurrency traders and early adopters in development. With the rise of NFT’s, smart contracts and dApps (decentralised applications), global interest and adoption/test projects have soared as the business opportunities for Web3 are clearly there.
The WEF describes this shift and the impacts as, “The current internet, Web 2.0, relies on systems and servers owned largely by big corporations, raising concerns over system vulnerability and control. When Meta’s associated platforms suffered a global outage in early October – exacerbated by the centralization of its servers – there were calls to adopt Web3 and its decentralized architecture.”
Applications of Web3 beyond cryptocurrency.
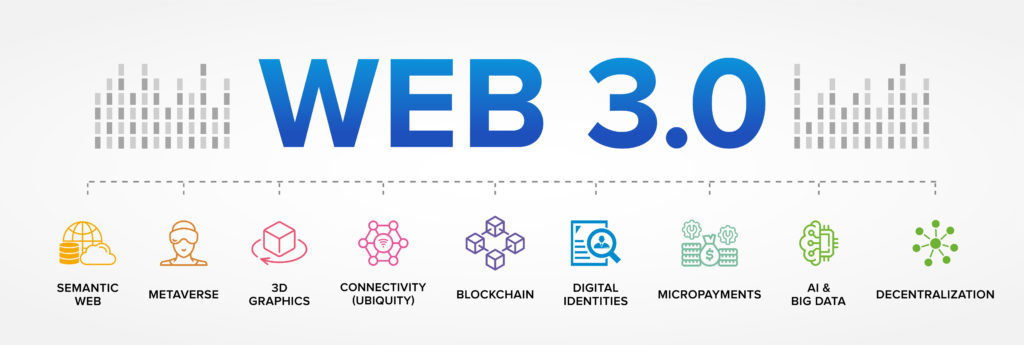
It could be said Web3 is already well out of the niche box in terms of the scope of its impact on the day to day lives of technological societies. Nine countries already have adopted Central Bank Digital Currencies (CBDCs), Apple’s Siri is Web3 AI technology, and many online games are making use of Web3 3D Graphics. The metaverse as a concept is entirely nascent of Web3 technologies and the adoption of the name Meta by Facebook was seen as a signal by many in the industry of a lean into the Web3 concepts of :
- Semantic Web. One of the key elements of Web 3.0 is “semantic web.” Tim Berners-Lee coined the term for a web of data that can be processed by machines.
- Artificial Intelligence.
- 3D Graphics.
- Ubiquitous (connectivity).
The above concepts clearly have broad applications for business in finance, services, and entertainment, so how will this be managed if not by private corporations and the governance relatively recently put in place to protect user data and privacy?
Governance in decentralised applications.
There are already examples of decentralised governance within the infrastructure of Web3, with Smart Contracts executing network rules in applications that have been voted for by stakeholders in any given project, through the Decentralised Autonomous Organisation (DAO) model. This system requires user participation and would mean assets or functions can be chosen or traded by the users rather than shaped or influenced by a large companies preferred direction.
The question for regulators will be how to hold DAOs to account if the governance does not belong to or reside not only in any one place as per Web2 companies, but with any one person or leadership.
Cybersecurity benefits and concerns in Web3
We have already touched on the potential implications if large private super servers are to become a thing of the past. The benefits of failsafe against server down time and direct hack would be substantial in protecting against market fluctuation or even cyberwarfare.
However, the risks of fraudsters and phishers inserting themselves within the network of anonymised users is also a real one. DApps are potentially the future of lightweight and versatile web functionality but without transparency of ownership or ways to vet participants you could potentially be collaborating with bad actors via the anonymised network.
Phishing scams are also possible and may take on a much more complicated turn if artificial intelligence is used to mimic secure sites and scalp information on 2FA and other login details of users. A Forbes article from May 2022 cites some huge phishing scams on non-fungible tokens (NFTs) and a 51% scam where $72,000 of cryptocurrency was double spent via a hack directly into the Ronin blockchain system.
Crypto jacking is also a vulnerability of this new technology. Hackers are not going for traditional targets such as user data, rather they are using their system’s dedicated hardware to mine cryptocurrencies without the user’s knowledge, potentially causing a huge spike in electricity consumption and straining expensive hardware like dedicated graphics cards.
If done to a company reliant on these systems you could be vulnerable to loss of hardware and subsequently data, or be forced to pay huge electricity bills so it’s worth your cybersecurity team or person being aware of this as a risk, especially if you are using a networked system with GPU’s for video and streaming.
While some of these risks may seem somewhat distant now, awareness of the benefits and vulnerabilities will enable you to stay ahead of the threats as they emerge and assess how they will impact your security if you venture into Web3 projects.
Here at Pie Security, our mission is to make your email security and privacy as easy as - well, pie.
Our founders, with 75 years of combined industry experience, provide leading email hygiene and encryption solutions for business, education, and government to help them comply with EU & UK privacy laws and GDPR.
Our blog provides easy to digest industry insights, email and cyber security guides, information and best practices for business.
Get in touch for a demo of our email and security solutions.
Tools like PieSecurity are designed with security and simplicity in mind. Learn more about our email hygiene and encryption solutions and how they can protect your business.
