Top cyber security trends of 2022 – an SRM leaders guide
Security and risk management (SRM) leaders will be more than familiar with the feeling of playing ‘whack-a mole’ with emerging cyber security threats. However, post-pandemic 2022 has been no ordinary year. The evolution of the cyber security role is evident, and the board and public’s perception of risk are beginning to align which has created a culture of cybersecurity and need for transparency and awareness. Bad actors and online threats have found even more areas of exploitation and vulnerable surfaces of attack within the digital infrastructure of companies and leaders need to stay agile and adaptable when supporting their team in the mission to keep ahead of the hackers and scammers.
In our recent articles we have focused heavily on user-end awareness, training, and cohesive cyber security policy as foundational in risk management and protection against data theft, corruption, or loss. These practices are essential, but they need to be supported by empowered and up to date thinking from CEO’s and SRM leaders. No matter the size of the organisation, the positive attitude towards adaptable cyber security and awareness and a respectful fear of the damage it could do to a business should be visible and clearly communicated from the top down.
The MSP Threat Report 2022 cites two in three mid-size organisations as having suffered a ransomware attack in the last 18 months. If that wasn’t reason enough to be concerned 20% of these companies spent at least $250,000 to fix the problem.
Some ways you can show leadership through awareness of the issues as they arise, is to provide a summary of potential areas of concern raised by your CIO, CTO, and IT team and to keep your policy and training up to date with new information on threats as they appear. If you are a small organisation without these roles, then it is still essential that there is direction from leadership in making your team members aware of relevant emerging threats and hacks that you are vulnerable to, as the impetus will be on everyone to keep up to speed. See our article ‘Keeping up to speed with cybersecurity’ for more information and ideas to help your team.
Below we have created a summary of some important vulnerabilities and cybersecurity trends that have emerged in 2022 that in turn can be used as a starting point for information you can share with your team.
Summary of important cybersecurity threats and trends of 2022
The Gartner research paper published in January 2022 highlights cybersecurity as becoming a social phenomenon. Stakeholders at all levels increasingly want visibility and reassurance that their information and assets are secure and align with their environmental, social and ESG governance requirements. A key finding of this report was, “Traditional culture improvement efforts that focus exclusively on awareness are failing to facilitate secure behaviour and have led to loss of control amid an increasingly distributed ecosystem.”
Essentially the more we work in different ways, the reliance on a culture of awareness cannot be the sole bastion against emergent cyber security threats.
Recommendations
As a security and risk management (SRM) leader, you should:
- Incentivise business executives to regard cybersecurity as one of their strategic business goals by ensuring that the board is reviewing outcome-driven cybersecurity performance reports.
- Reinforce desired executive cybersecurity risk behaviour by working with the human resources (HR) team to insert cybersecurity performance goals in business executive employment agreements.
- Reduce your organization’s potential for negative societal impact by developing environmental, social and governance goals (ESG) as part of your annual cybersecurity strategic planning.
- Define the scope and objectives of your third parties. For some, this might just be the critical IT vendors while for others it might include the entire ecosystem, such as individual customers/citizens or subsidiaries.
- Ensure cyber risk quantification is outcome driven. Clarify the specific business decision you want to influence and make quantification outputs directly actionable for decision-makers.
Source: Gartner 2022
Strategic Planning Assumptions
By 2026, at least 50% of C-Level executives will have performance requirements related to cybersecurity risk built into their employment contracts.
By 2025, 60% of organizations will use cybersecurity risk as a significant determinant in conducting third-party transactions and business engagements.
By 2025, 50% of cybersecurity leaders will have tried, unsuccessfully, to use cyber risk quantification to drive enterprise decision-making.
By 2026, 30% of large organizations will have publicly shared environmental, social and governance (ESG) goals focused on cybersecurity, up from less than 2% in 2021.
By 2025, 40% of programs will deploy socio-behavioural principles (such as nudge techniques) to influence security culture across the organization, up from less than 5% in 2021.
Source: Gartner 2022
Outcomes and analysis
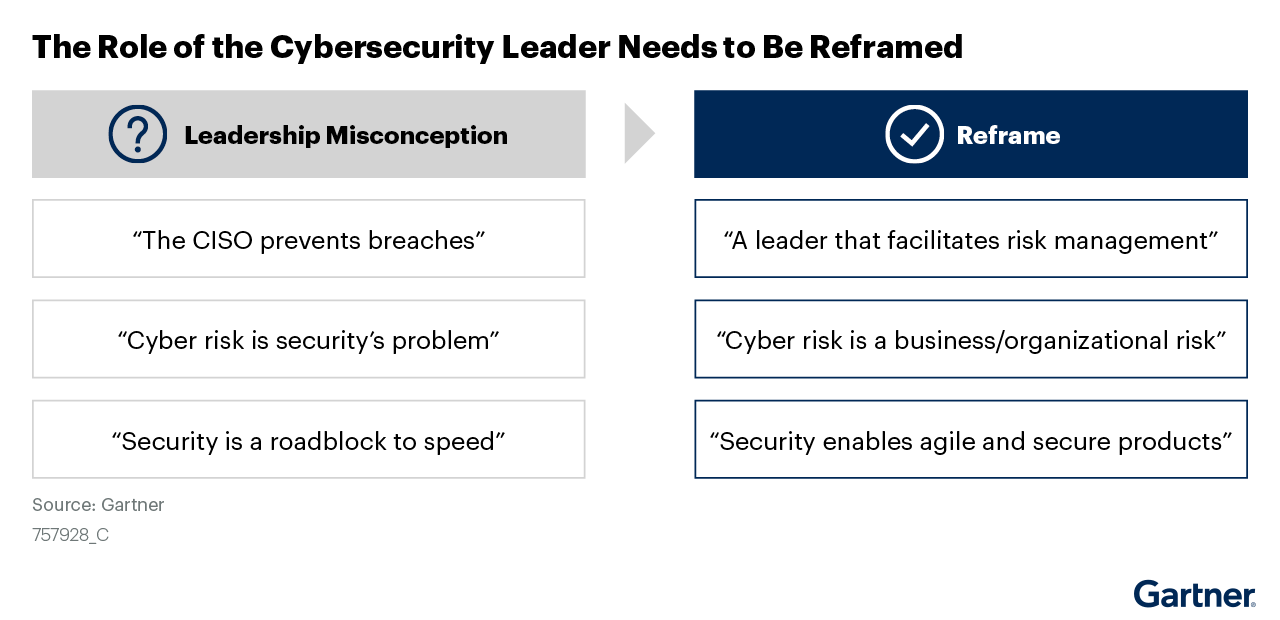
Analysts at Gartner have described the elastic nature of cybersecurity leadership roles as having created an ‘always-on’ workplace culture due to growing misalignment of expectations from stakeholders within the organisation. 88% of board members now see cybersecurity as a business risk not an IT problem so this misalignment appears to be shifting. Further new concepts that SRM leaders will need to be aware of and communicate are:
- Resilience and risk quantification
- Increased levels of digital connections forcing organization to put significantly higher levels of effort into controlling (evaluating, influencing) the cyberhealth of external parties
- Employees now making decisions with cyber risk implications without consulting security and risk management leaders
- Executive committees being established outside the scope/purview of the cybersecurity leader
These factors will reduce the direct control over many security aspects that SRM leaders have generally had until now. This reframing of the role is summarised in the figure below.
Want to take control of your organisation’s digital security? Book a Demo now and hear how Pie Security can help you create confidence in your product with our email encryption tool and compliance assessment.
